Dear Community,
In my system 10 Domino servers are registered, all running Domino 9.0.1 FP8 or FP9 or FP10.
Adress book has about 2 100 users.
names.nsf (and some other system db) is replicated to all servers in the domain.
Policies use ID Vault.
All users have a 630 bits certificate.
Prior to the Domino V11 deployement, I have decided to upgrade these keys to 2048 bits.
I do know that Domino V11 will work with 630 bits and requires 1024 for new users.
The fact that 2048 has been choosen has nothing to do with my problem, hasn't it ?
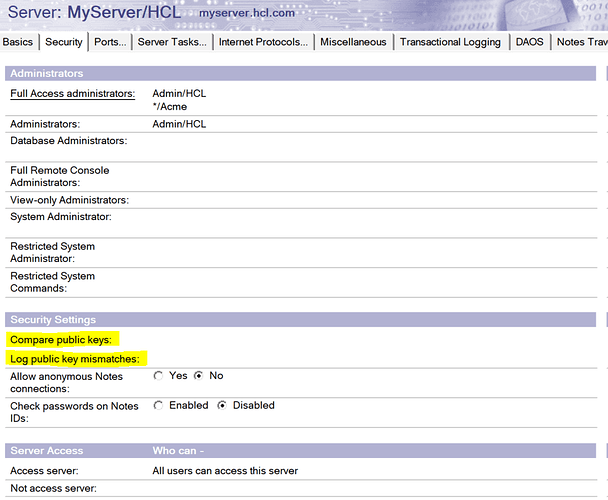
Registration policy settings document has been set to use a public key of 2048 bits
Security policy settings document has been set to 2048 bits.
For this document I also set the following fields "Spread new key generation for all users over this many days": 15 days.
Things went well:
New users are creating with a 2048 key length and request for new key appear in the Administration Request database (admin4.nsf).
I have noticed that recertifying a user whose does not give a 2048 bits key but keeps on with the 630 one. These users are not (yet) in the admin4: they are just people whose certificate comes to end.
In order to do this I follow instructions found on https://help.hcltechsw.com/domino/11.0.0/conf_assigninganewkeypairtoacertifer_t.html
This link is related to V11, but in my understanding this is also valid on previous version, at least for Domino 9.
Then, things went wrong.
Many actions related with the ID Vault do not work anymore or as expected.
1. User creation: policy using the ID Vault gives an error while putting the newly created user in ID Vault.
Workaround: a new policy which do not use ID Vault
2. User deletion : I didn't test this but assume it will give the same error.
Workaround: I just put users in deny group.
3. Password reset: it is no more possible to do it with the ID Vault tool
Workaround: downloading user's ID from the ID vault is still working. I just give a new password and put the ID in the user's environment. It appears that ID replication with ID Vault is still working.
There are a couple of error messages:
Error processing certificate created by /***** for *********/*****: The signature on the certificate was found to be invalid. Check the log file for details.
Log ? Which log ?
Personnal log ? This message comes from the personnal log.
Server log ? Nothing found.
Certlog ? Last record for this user doesn't show any problem (never see an error message in the cerlog btw).
This is not preventing me for logging or working (excepted for above actions).
23/03/2021 08:54:12 ********** ************/****** from host [***.***.***.***:***] failed to authenticate: Your public key does not match the one stored in the Address Book
Analysing such messages shown me that for some users keep on working and this error message just go away after some time.
For other users, they cannot log any more.
Workaround:
On user's environment, File/Security/User Security/Your Identity/Your certificates/Other Actions/Mail Copy Certificate (Public key).
I just set the user's public key stored in the user's document on the adress book with this key.
23/03/2021 11:18:04 ID containing certificates for new keys for ************/***** marked for backup
What does the message means ?
Key in user's document is 2048 length.
Is it done ?
Found in admin4.nsf
Title: server adress book name Path: names.nsf; Error: Object validity dates not within specified time range
What does the message means ?
I have contacted my local IBM/HCL Reseller and Service Providor.
I have been proposed to restore names.nsf !
Worst case scenario and certainly not without a fight !
Does anyone can explain me what happend and what did I do wrong ?
What should be done in ordre to get back to a correct situation ?
Thank you very much for any comment.